How to check if an Android app is safe to install
Android devices are among the most popular devices on the market today. With a wide variety of features and designs, users have an abundance of choices. Not only that, but there are also more than two million apps available on the Google Play Store. Unfortunately, some of these are rogue software developed by cybercriminals under […]
Read MoreWhy business continuity plans fail
Even the best managed IT services provider (MSP) can overlook certain business continuity plan (BCP) details. This is why businesses should always be on the lookout for the following pitfalls of BCP to ensure that the plan works as it should. Over-optimistic testing The initial testing attempt is usually the most important, because it’s when […]
Read MoreAre your mobile devices protected?
Mobile devices are indispensable. Smartphones, tablets, and other mobile gadgets play a big part in everyday processes, especially for individuals and companies that value connection and convenience. But as the number of mobile devices used in business operations increases, so do the cyberthreats that target them. Be sure to follow these steps to safeguard company […]
Read MoreWhy does HTTPS matter?
Most people don’t question the padlock icon that sometimes appears in their web browser’s address bar. If you’re one of those who didn’t know, it’s a security feature that authenticates websites and protects the information users submit to them. Another indicator you’re in a secure site is the HTTP before the site’s URL. But why […]
Read More8 Ways Excel Fails at Stock Management
Tracking your company’s stock with a spreadsheet is costing you big bucks. Logging inventory cycle counts with Microsoft Excel may seem like the least expensive approach. But in truth, it would be cheaper to buy an automated inventory management system than to continue using your Excel spreadsheet. Why waste time and money? Consider these eight […]
Read More3 Ways To Stop Cybercriminals during a pandemic
In the past couple of months, just about everyone has been forced to shift priorities. If you’re like many business owners, you are intently focused on pivoting your business to accommodate today’s “new normal.” In fact, you are probably investing so much of your time in trying to retain your customers and generate new cash […]
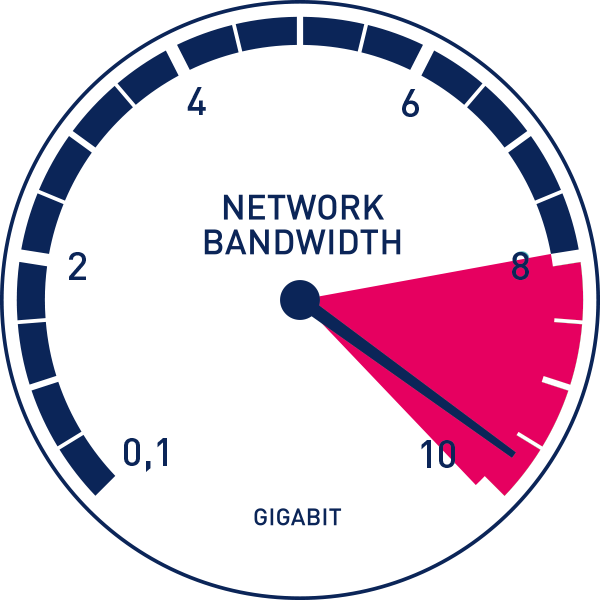
Read MoreCan your internet bandwidth handle remote work?
Even before COVID-19, remote working was already quickly becoming the new normal. It took a pandemic to tip the scale, and now most jobs are being done from home. But it’s not always a smooth ride. There are many things that can cause productivity dips, one of them being limited internet bandwidth. How much bandwidth […]
Read MoreMicrosoft Teams boosts productivity in spite of COVID-19
More and more people are forced to work from home to avoid the COVID-19 pandemic. But Microsoft Teams is rising to meet the needs of affected companies. This powerful tool recently underwent several changes to make it easier for its users to effectively collaborate and communicate with each other. What is Microsoft Teams? Microsoft Teams […]
Read MoreOptimize inventory management with ERP
Keeping your inventory under control has never been so important. Customers aren’t willing to settle for “close-enough” any longer. They can search the internet for exactly the model and features that they need and often purchase directly from the source. The success of your retail, distribution or manufacturing business depends on having the right stock […]
Read MoreA smart approach to cybersecurity investment
Cybersecurity is a threat to businesses across industries. Sometimes, organizations invest in security software without realizing the risks that come with it. Here are compelling reasons why identifying threats before buying cybersecurity products is paramount. Uncover threats and vulnerabilities Every business should run a risk assessment to evaluate its current cybersecurity infrastructure. Doing so is […]
Read More